Reverse engineering
Reverse engineering is an activity whose objective is the study and analysis of a system in order to deduce its internal functioning.
In computer science, the objective of software reverse engineering is to to study a software without having its source code available, with the aim of:
- understanding how to block or disarm a malware,
- discovering and fixing software vulnerabilities.
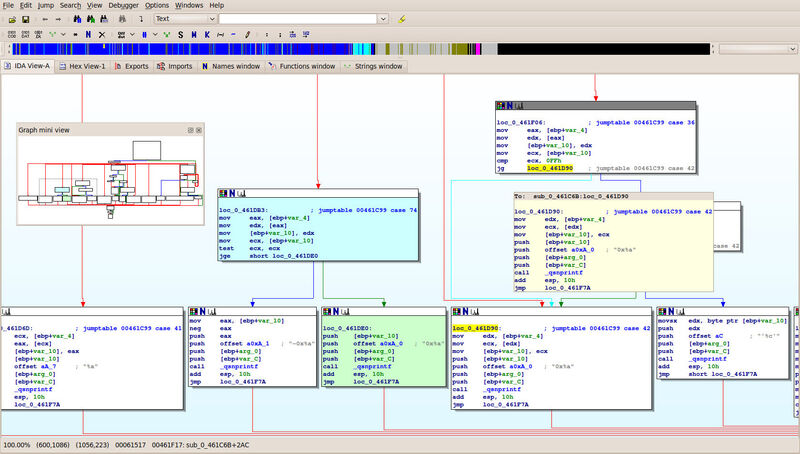
To do this, we use tools such as disassemblers, decompilers, debuggers, binary file editors... but we also need skills! One must know how to develop, know the technical specifications of the target processors (x86, RISC, ARM...) and operating systems (Unix, Windows, Android...), know the compilation mechanisms and software protections (Packer, AntiDebug, AntiSandbox, DEP, ASLR...), and above all, be a curious person.
Whether it's on your network, computers, servers, mobiles, we're able to reverse engineer a lot of applications.
Malware analysis
If machines in your infrastructure are infected with malware, the malware may be:
- a backdoor, allowing an attacker to take control of your systems,
- a ransomware (or crypto-locker), that will make your files inaccessible by encrypting them,
- a stealer, that will steal data from you,
- a rootkit, that will disguise the activity of an attacker on your machines,
- and any other type of malware that causes damage to the availability, integrity or confidentiality of your data.
In order to be able to eradicate it, we will study how it functions in a confined environment, in order to understand how it settled, spread, and persisted.
With the knowledge acquired in the study phase, we will determine a way to disarm it, either by blocking its operation or by completely uninstalling it, and thus establish a cleaning procedure.
Other people in your company will then be put in the loop, such as system and network administrators, in order to apply these cleanup procedures, but also to make changes so that installing such malware will be made impossible or very complicated in the future. This includes the identification of markers or artefacts identifying the malware, which are then transmitted to a SOC. It can be configuration adjustments to the machines, addition of technical protection measures, or behavioral changes.
If we take the example of an email phishing campaign, which is the most common vector of malware propagation in companies, three solutions can be implemented to try to avoid, or at least reduce the chances of a second infection:
- configuration adjustments: disabling extensions commonly used to propagate this type of threat (.vbs, .hta...)
- adding technical protections: proactive or reactive measures (antivirus filtering, sandbox solutions, HIPS, EDR, SIEM...)
- behavioral changes: security training for regular staff and fake phishing campaigns
Enhanced software security
Software security is an example of the usefulness and necessity of reverse engineering. Whether it's because of a design flaw, a poor implementation, or a lack of testing, software often comes with a lot of vulnerabilities. These vulnerabilities can have a significant impact on the security of your data, software, or your business model. Reverse engineering can help uncover such security holes and address them.
When a software company wishes to test the security of its solution, it can use several methods or strategies to estimate its reliability. These evaluation techniques inevitably include audits on targeted or broader scopes. The following audit strategies can be used:
- audit all or part of the application's code: it will improve the quality of the code rather than its security, given the considerable work involved
- audit the software architecture: libraries used, reliability of authentication methods, encryption mechanisms, robustness of APIs...
- audit the hardware and software infrastructure on which it rests
All of the above strategies are good practice and each have relevance from a software security perspective. It is these types of audits that allow the ANSSI to certify products (CSPN, EAL3+, EAL4+). These certifications are then valid for a specific version of the solution, and attest to a specific level of security, corresponding to the means and skills of an attacker.
Among the techniques discussed, one of the most time-consuming and technically demanding is the search and exploitation of vulnerabilities. This is a very targeted activity (specific product version and installation environment) which is an essential complement to the software code audit. It often applies to only one component of the application, because working on the whole application can be a daunting task. Reverse engineering skills are essential. The vulnerabilities we're looking for in this phase can be of any type:
- logical bug: error in the program logic, for example being able to authenticate with an empty password
- stack buffer overflow: allows an attacker to write to a memory area used by a program and modify its behavior
- heap overflow: similar to stack buffer overflow but harder to exploit
- use-after-free: faulty program behavior that reuses a memory area previously manipulated by the attacker
- race condition: bug causing the program to behave potentially badly depending on the order in which the instructions are executed
- time-of-check to time-of-use: allows an attacker to alter the contents of a memory area between its validation and use by a program
Vulnerability scanning usually begins with a step of fuzzing (with tools such as Peach Fuzzer or American Fuzzy Loop) in order to determine which user inputs cause the application to crash, see if they can be exploited and under what conditions. It is therefore necessary to be familiar with the installation environments and the protections implemented natively (DEP, ASLR, stack canaries...)
A necessary step of reverse engineering will then determine the type of bug and its operating conditions. This will allow developers to fix the vulnerability, and to estimate vulnerable installations and versions of the product based on the system environment on which it was installed. The vulnerability disclosure process is framed, and may result in the release of a CVE (Common Vulnerabilities and Exposures).
When an unknown vulnerability is exploited by a group of attackers, without the editor knowing about it and being able to patch it, we then talk about a 0-Day.
Forensic investigation
Forensic investigation is an activity primarily carried out by law enforcement and incident response teams. It's about collecting, analyzing and preserving all digital traces deemed necessary to determine, identify, prove, disprove a thesis or an element.
The proof can therefore be presented in multiple shapes. It is therefore necessary to use reverse engineering techniques for the following purposes:
- search for exploitable traces or artifacts
- analysis of encryption mechanisms (BitLocker, dm-crypt, LUX, VeraCrypt, TrueCrypt...)
- analysis of proprietary file formats
- analysis of artifacts on various storage systems
- analysis of artifacts within RAM
- reverse engineering of an exotic operating system, industrial equipment, or IoT
- identification of the causes of an artifact's presence
- analysis of the software or mechanism that produced the artifact
Other pages that might interest you :
Cybersecurity contracting authority support
We help you integrate security at the beginning of your projects.
Active Directory securization
We help you secure your Active Directory through audits and technical assistance.
Ransomware assistance
We explain what are ransomware, how they operate, what you can do when you're infected, and how to prevent them.
Specialists in information security and pentest in Lyon, Paris, Saint-Etienne and throughout France
You've enabled "Do Not Track" in your browser, we respect that choice and don't track your visit on our website.