What is an internal intrusion test?
The security of your computer network can be compromised by external attackers, but also by internal attackers Our internal penetration tests allow us to evaluate the impact of an attacker on the elements of the information system accessible from the company network. Unlike a Red Team audit, only the security of IT resources is evaluated, not the security of physical premises or personnel vigilance.
There are two types of internal audits:
Internal audit in black box evaluates threats related to an attacker connected to an Ethernet socket, without user account. We sometimes call it a 'plumber's audit'.
Internal audit in grey box evaluates threats from an attacker with a user account with standard privileges. We sometimes call it 'trainee audit'.
The common prerequisite for both types of tests is to be able to connect to an Ethernet socket on your internal network and not be blocked by a Network Access Control (NAC) device, such as 802.1X. We can also perform this LAN audit from a user station.

Internal pentest process
The process of our audits and pentests is based on the PTES (Penetration Testing Execution Standard), and aims at performing an audit in the time optimization. Furthermore, we respect the perimeter that you impose on us in terms of targets, time range, or type of attacks.

We begin with a phase of enumeration, during which we discover the services and machines exposed on the network range we are connected to, and then we repeat this process to other networks in your company. We use the well-known nmap tool, but also other tools and scripts of our own design to speed up this process.

Once we have a synthetic view of the main networks in your infrastructure, we exploit the flaws allowing us to elevate our privileges and retrieve confidential and sensitive data. Please note that if you have a very large internal network, you can give us the main networks on which you would like us to focus our attention.
At the end of the audit, we'll take a moment to discuss the key findings with you. The idea is to give you a synthetic view of the main risks to your internal network: what are the main impacts of the discovered vulnerabilities on the security of your data, the level required of the attacker and the complexity of the attacks to be carried out. We then continue with the writing of the report.
Once we have sent the report, we'll plan a presentation. The objective of this step is to present both a managerial vision of the audit results, but also a detailed technical vision. This is why we encourage you to invite your technical teams to this exchange, so that they can be informed of security defects and the corrective actions we recommend.
Of course, the auditors remain at your disposal even after the restitution, by email or telephone, to answer your questions or to advise you on the implementation of corrective actions. We aim to establish a relationship of trust as well as long-term accompaniment.
Main defects tested during LAN audits
The defects listed below are indicative, and the knowledge of our auditors is constantly evolving to keep up with new attacks.
File sharing is commonly used in companies so that users can share documents with each other. However, these are frequently misconfigured, and overexposed. For this, we check, among other things:
- that your network has the minimum of file shares accessible without a user account,
- that the highly vulnerable SMBv1 protocol is no longer used or enabled,
- that no sensitive or confidential data is stored on file shares accessible without a user account,
- that access rights to file shares be granted consistently, and preferably by group rather than by user.
If necessary, our report will include the list of discovered file shares, and the access rights to them.
Windows mechanisms allow a user to authenticate to a server or service by sending an authentication sequence, rather than just a username and a password. However, due to poor configuration, an attacker may be able to eavesdrop on network traffic and retrieve these authentication sequences in order:
- to crack them in order to recover the user's unencrypted password, especially when the password policy is weak or non-existent,
- to relay them to one of the other services, without having to crack them, in order to gain access to those services illegitimately.
For this, we check, among other things:
- that the most recent authentication sequence protocol, NetNTLMv2, is selected,
- that user passwords are not stored in clear text in machines memory, via WDigest for example,
- that Microsoft's name resolution protocols, LLMNR and NetBIOS, are disabled in favor of DNS,
- that hosts on the network check the SMB packet signature,
- that the IPv6 protocol, if enabled on the hosts, is handled correctly,
- that a strong password policy is enabled to make it more difficult to break authentication sequences.
Exchange servers, because of their importance and functionality, are generally installed by default with a configuration that grants them significant rights to Active Directory objects. Through other vulnerabilities, an attacker can manipulate Exchange servers and their high privileges in order to perform sensitive actions, or grant high privileges to an account. For this, we check, among other things:
- that the Exchange servers are up to date and have the latest security patches installed,
- that the privileges granted to Exchange servers are reduced to the minimum necessary to function,
- that the network flows are properly managed so that an Exchange server cannot authenticate to a user workstation,
- that obsolete Windows protocols such as MS-RPRN are disabled.
Active Directory and Windows networks administration is complex, especially due to the strong evolution of these technologies, as well as the need for Microsoft to maintain backward compatibility of these solutions for businesses. However, new protocols, solutions and architectures have emerged to fix the many critical vulnerabilities found in these systems. Unfortunately, many times they are not implemented due to lack of knowledge, time or resources. For this, we check, among other things:
- the attack paths that would allow a standard user to elevate their privileges to domain administration,
- the application of patches to protect against recent vulnerabilities such as BlueKeep, EternalBlue, PrivExchange, MIC-Remove, Kerberoasting...
- the implementation of best practices such as LAPS (Local Admin Password Solution) or n-tier administration.
Solution integrators rarely take security into account, and installed products generally have neither an upgrade policy nor a password policy. For this, we check, among other things:
- that access to the administration interfaces of the different services is not possible from the standard users networks,
- that access to the administration interfaces is secured with a strong password and that the default passwords are changed.
- that solutions and services are up to date and have no known vulnerabilities and can be easily exploited.
These security defects are present in the vast majority of internal networks built with a Active Directory, and they are also the security defects with the highest impact on the security of the information system. During a LAN audit, we also perform service-specific tests: iSCSI, FTP, SMTP gateways, SQL and Oracle servers, SNMP, SSH, RSH... within the time limit of the audit.
Main tools used
We use tools that are mainly open-source, with a high level of quality and a strong reputation in the cyber security community. We can quote, but not exhaustively:
- ACLight, ADRecon, BloodHound for mapping Active Directory objects,
- CrackMapExec, Impacket, Mimikatz, Metasploit for offensive actions,
- Hashcat, JohnTheRipper for password-cracking,
- nmap, unicornscan for port scans and services identification.
We also use an internally developed tool, Pollenisator, to facilitate the management of scans during a LAN audit and traces between auditors.
We like to highlight the transparency of actions taken on your infrastructure. For this purpose, you will find in the appendix of our reports the list of tools that were used during the audit, as well as any script that we may have developed for a specific need.
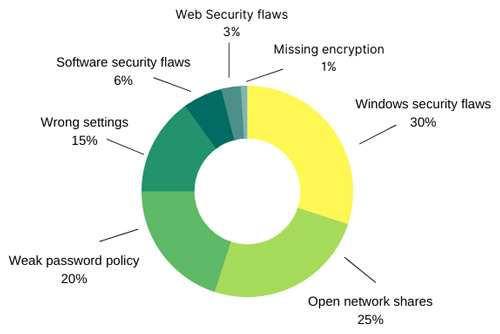
Most common attack vectors
Below is a graph showing the most common attack vectors, from our experience during internal pentests.
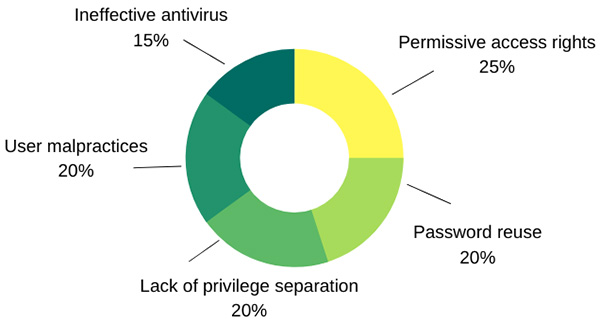
Most common facilitating elements for attacks
Below is a graph showing the most common facilitating elements for attacks, from our experience during internal pentests.
Specialists in information security and pentest in Lyon, Paris, Saint-Etienne and throughout France
You've enabled "Do Not Track" in your browser, we respect that choice and don't track your visit on our website.