The brute-force attack is one of the simplest intrusion methods, but also one of the most formidable. And why? Because it requires very little experience on the part of the cybercriminal, is automated and exploits human weakness above all else. Passwords are all too often predictable, providing an ideal entry point.
But its impact doesn't stop at simply stealing credentials. bruteforce attacks are often used as leverage for other attacks, exploiting insufficiently patched security flaws. That's why it remains an essential tool, both for malicious hackers and for pentesters seeking to identify system vulnerabilities.
How it works: test as many combinations as possible until you find the right one. These attacks are automated, making them even faster and more effective. Despite its age, this method remains a mainstay of cyberattacks on systems and networks.
This article is an introduction to brute force attacks. Although some of the techniques presented here also apply to cracking encrypted passwords or other attacks, this article is intended to focus primarily on bruteforce attack techniques against services exposed on the Internet.
In the first part, you'll find a reminder of the basic concepts of bruteforce attacks, followed by a presentation of the tools commonly used, patches and existing protections and finally methods for circumventing them. Finally, we'll share our experience in developing these attacks.
Brute force attacks
Brute-force attacks are a common method in the cyber-attack landscape. They consist of trying a large number of possible combinations to unlock a security system by coming across a valid combination. The same method is often used to crack hashed passwords during offline brute force attacks. This technique can be particularly effective on poorly protected systems or weak passwords.
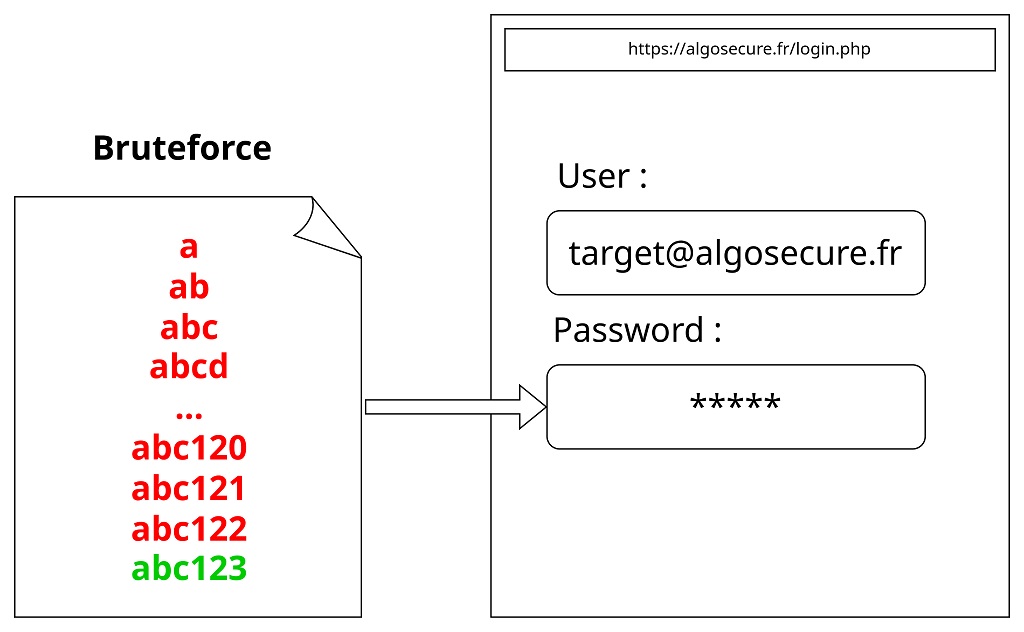
Testing all character combinations can be inefficient, however, as the number of combinations to be tested is exponential to the number of characters to be tested.
An attack on 6 lower-case alphanumeric characters (i.e. in our case 36 characters) allows 36⁶=2,176,782,336 possible combinations. Adding a single character (so 7) increases the number of combinations to 36⁷=78,364,164,096, or 36 times more. A few extra characters can turn an attack lasting a few seconds into one lasting several decades.. This number may also depend on the number of characters allowed.
This is why there are several bruteforce techniques, to reduce the number of combinations to be tested with a view to having a successful attack in a reasonable time.
Dictionary attack :
Rather than testing every possible combination of characters, the dictionary attack relies on predefined lists of common words and frequently used passwords. The aim is to test all the passwords in the list for each target. Attackers rely on the fact that many users choose weak or easy-to-guess passwords, such as words from the dictionary, names or strings of numbers.
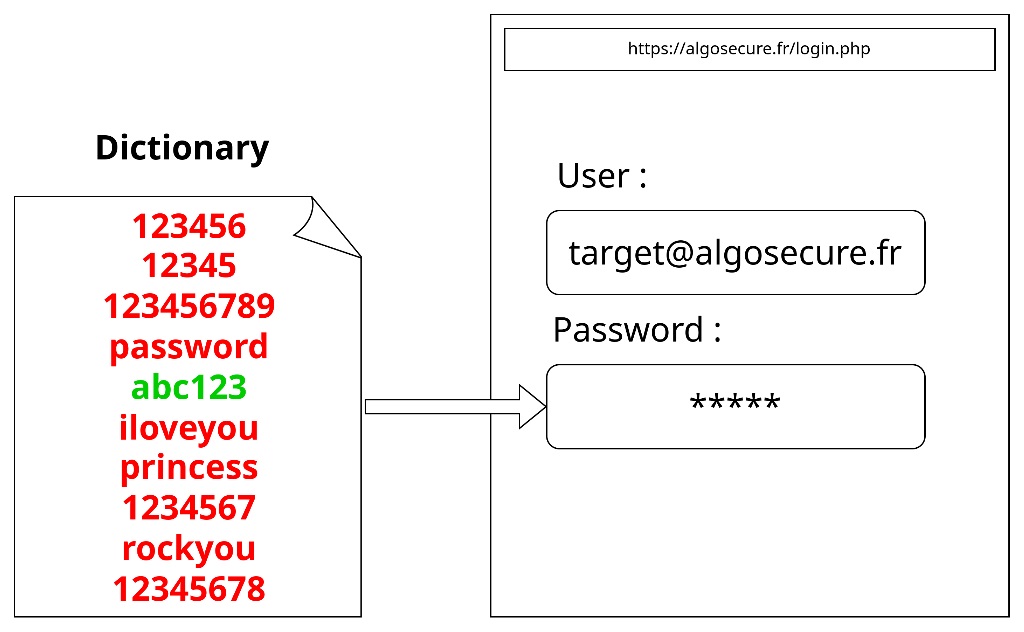
Many dictionaries are available for download. We recommend the SecLists which offers several comprehensive dictionaries.
For more specific needs, you can create your own password lists using a variety of tools. These include Cewl, , Crunch, , Bopscrk, , John the Ripper...
Password spraying :
Unlike the dictionary attack, which targets a single account at a time, password spraying attempts common passwords on many different accounts, with the hope that at least one of them will use a weak password. This technique is particularly used against systems with protection against repeated attempts on a single account.
Warning: It is recommended to check the password policy first to avoid account blocking.
In our experience, many companies tend to use easily predictable passwords. These are usually composed as follows:
company name or acronym predictable number (e.g. 123) or date or company department number sometimes a special character (usually "?" or "!")
Following this logic, for the "algosecure" company, the following dictionary can be created:
Algosecure2024!
Algosecure69?
Algosecure123+
Algo123!
…A password dictionary with these features can easily be created with "rules".
For example, the command below creates passwords using John the Ripper's "Wordlist" rule.
john --wordlist=pass --rules=Jum --stdout
…
algosecy
algosec123
algosecman
algosecdog
thealgosecure
magosecure
alsecure
algs
algos1
algosecu
algosecalgosec
…Password leakage :
This approach relies on exploiting databases of compromised passwords, often the result of data breaches. Attackers retrieve this information, often available on the dark web, and attempt to use it on other services. Indeed, users often use the same password on several platforms. There are a number of tools available to determine whether a password leak linked to an account exists.
The platform https://haveibeenpwned.com allows individuals to find out if their login details are present in one or more data leaks.
For professionals, we offer our AlgoLightHouse which allows you to retrieve the passwords in question from several private databases or from information available in discussion groups on chat forums.

Some tools
When it comes to implementing brute-force attacks, several tools are commonly used by cybersecurity professionals. Here's a brief overview of three popular options: Burp Suite, Hydra and custom scripts.
To take an example, let's look at the following site:
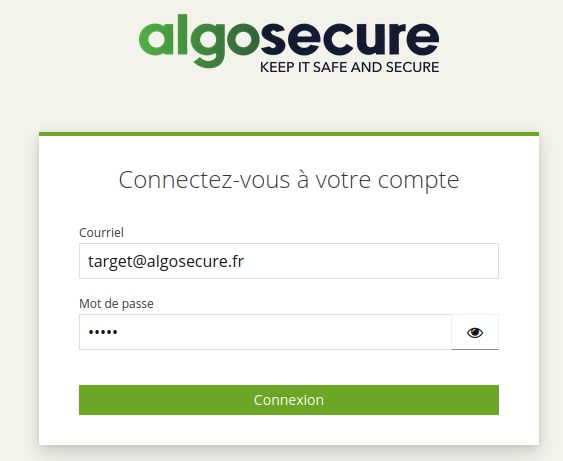
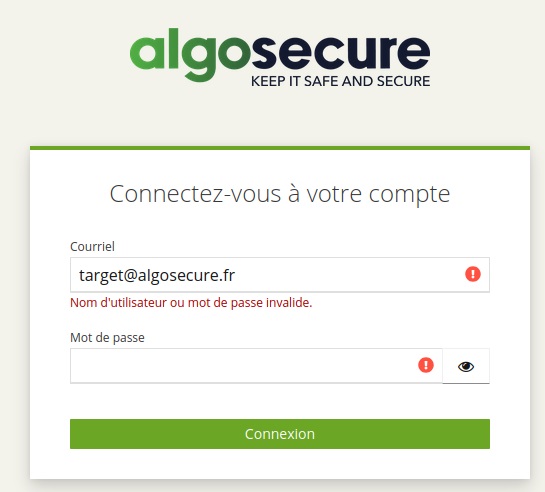
Here, the attacker wants to connect to the target@algosecure.fr
The query associated with the connection attempt is as follows:
curl -d "username=target%40algosecure.fr&password=*****" -X POST https://algosecure.fr/login.php
Burp Suite
This tool is mainly used for security audits of web applications. It features a wide range of functions, including a module for brute-force attacks. Thanks to its intruder, Burp can automate the process by testing several combinations of passwords or queries on login forms or other sensitive entry points a web application.
Burp's interface offers a fast, intuitive solution for web applications. Once the request has been intercepted, all you have to do is use the "Intruder" module, define the area of the request to be substituted by the various passwords to be tested, and select the file to be read on the fly.
Once the attack has been launched, simply search for the query whose result stands out from the erroneous queries:

Here the status returned by the valid request is different.
The tool's many options include advanced filtering, data modification, bypassing anti-bruteforce mechanisms such as anti-CSRF tokens, and tracking redirects.
Hydra
Hydra is an extremely fast and versatile command-line tool for brute-force attacks on various protocols, such as SSH, FTP, HTTP, and many others. It is widely used for testing network authentication, offering great flexibility and supporting multiple services simultaneously. Hydra can also use password lists, such as those available in SecLists, to perform massive authentication attempts.
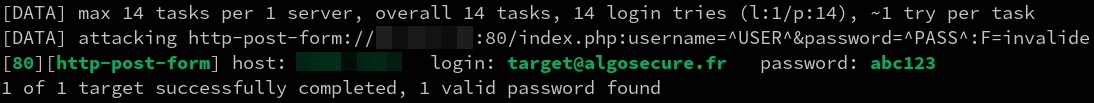
To repeat the example above, simply run the following command:
hydra -l 'target@algosecure.fr' -P dictionnaire.txt -f login.php http-post-form "/:username=^USER^&password=^PASS^:F=invalide"
The latter takes the .txt dictionary and highlights the password that has received a server response that does not contain the word "invalid".
Finally, this tool has the advantage of being compatible with many protocols other than http.
Custom scripts
For scenarios where pre-existing tools don't meet specific needs, writing scripts on the fly can prove useful. With libraries such as requests on python for interacting with APIs or web forms, or paramiko for SSH, custom scripts enable attacks to be precisely tailored to the target, automating tailor-made attacks with granular control.
The script below is an example of a python script for testing password combinations.
import requests
target_url = 'https://algosecure.fr/login.php'
dictionary_path = 'dictionnaire.txt'
try:
# Ouvrir le fichier de dictionnaire
with open(dictionary_path, 'r') as file:
words = file.readlines()
headers = {
'Content-Type': 'application/x-www-form-urlencoded'
}
# Pour chaque mot dans le dictionnaire
for word in words:
word = word.strip()
data = f"username=target%40algosecure.fr&password={word}"
response = requests.post(target_url, data=data, headers=headers)
# s’il reçoit un réponse positive
if response.status_code == 200:
print(f"mot de passe trouvé: {word}")
break
except FileNotFoundError:
print(f"Dictionary file not found.")
except Exception as e:
print(f"An error occurred: {e}")
This gives the following result:
Scripts, whether in Python or another language, are important because they enable us to carry out brute-force attacks when we find ourselves in a restricted environment. For example, it may be necessary to perform a bruteforce attack on an internal company application, from a compromised machine.
Some remediation techniques
To protect against brute force attacks, several remediation techniques can be implemented. The aim is to limit repeated attempts at unauthorized access, while minimizing the impact on legitimate users. Here are three commonly used methods: IP blocking, temporary account blocking and the use of multi-factor authentication.
IP blocking
This method consists of automatically blocking the attacker's IP address after a certain number of unsuccessful attempts. It has the advantage of being relatively easy to implement, often without requiring any changes to the application. Blocking can be carried out at server or firewall level, offering rapid protection against brute-force attacks. However, this method can be circumvented if the attacker uses multiple IP addresses or a botnet.
Temporary blocking of accounts
This method consists of temporarily disabling an account after several failed login attempts. It offers a higher level of security, as it prevents the attacker from continuing the attack without penalizing legitimate users in the long term. However, it is essential to configure this measure correctly to avoid disclosing information about the existence of accounts. Indeed, the system must react in the same way, whether the account exists or not, so as not to reveal to attackers the validity of an identifier. In addition, the duration of the block must be short enough to avoid affecting user productivity, while at the same time deterring brute-force attacks.
By combining these two methods, organizations can significantly strengthen their protection against brute-force attacks, while maintaining a balance between security and accessibility.
Multi-factor authentication (MFA)
Multi-factor authentication is one of the most effective solutions against brute-force attacks. It requires the user to provide a second proof of identity in addition to the password. There are three ways of proving identity. What they have (e.g. their telephone number), what they know (their password) and what they are (a biometric fingerprint). The use of MFA consists in using several factors, such as the password and a code received by SMS, which justifies that the user is in possession of his number. This considerably complicates unauthorized access attempts, as even if a password is compromised, the attacker will still need to obtain this second factor to successfully authenticate.
However, there are techniques for bypassing MFA, such as the phishing or social engineering, where users are encouraged to validate the MFA (MFA fatigue) or provide their second factor directly to the attacker. It is also possible to bypass this mechanism via attacks on services that do not correctly implement this protection (predictable or bruteforcing code). It is therefore important to combine MFA with other security measures to ensure maximum protection.
Some bypass techniques
Although the above-mentioned protection mechanisms can limit the majority of attacks, some attackers develop methods of circumventing these restrictions if they are not properly implemented.
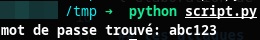
Use of botnets or IP rotating table
To circumvent restrictions based on IP addresses, attackers can use botnets, which allow attack attempts to be distributed across a network of infected machines each with a different IP address. Another approach is to use an IP rotating table, a pool of IP addresses that the attacker can easily obtain via services such as AWS or by creating multiple instances on platforms such as Scaleway. This allows IPs to be changed on each attempt, making IP blocking based on a limited number of attempts from a single address ineffective.
An extension is also available on the Burp tool: https://github.com/portswigger/ip-rotate. The latter makes it easy to interface with an API such as that offered by AWS.
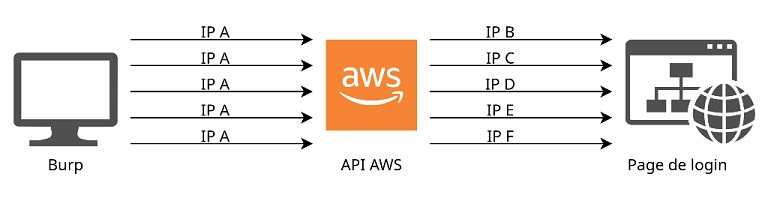
Exploiting the X-Forwarded-For header
The HTTP X-Forwarded-For header is mainly used in network infrastructures to inform servers of the client's true IP address when the client passes through a proxy or load balancing server. This header is added by the proxy or load balancer to inform the downstream server of the user's original IP address, which would otherwise be masked.
The diagram below shows how a request is sent through several proxies, without and then with the "X-Forwarded-For" header.
In the case of IP blocking, some systems must therefore rely on the original IP address to detect and block attackers. However, if the management of the X-Forwarded-For header is misconfigured, an attacker could exploit this weakness by injecting falsified IP addresses into the header.
By modifying this header, the attacker can trick the server into believing that each request comes from a different IP address, thus bypassing blocking restrictions based on a single IP address. This is particularly effective if the server accepts the header without checking its legitimacy or applying appropriate filtering.
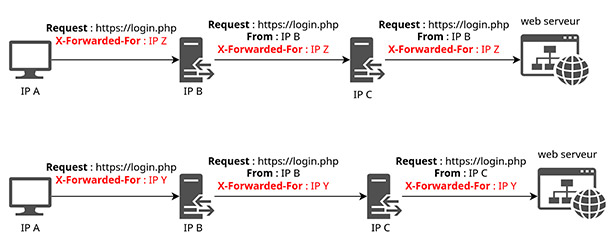
This type of attack is most effective when the server or authentication system fails to properly validate the X-Forwarded-For header, or blindly trusts the value provided. This is why it is essential that security systems do not rely solely on this header without applying additional checks. To mitigate this risk, servers must ensure that only trusted sources add this header (such as internal proxies or load balancers), and that any addition of this header of external origin is properly filtered.
Login with a valid ID at regular intervals
Another bypass technique consists in using a valid identifier after several unsuccessful attempts. This allows you to reset or bypass protection mechanisms that block after a certain number of unsuccessful attempts. By logging in with the correct information every "x" requests, the attacker can avoid reaching the blocking threshold, either at IP or account level. For example, a blocking threshold of three unsuccessful attempts can be bypassed as shown below.
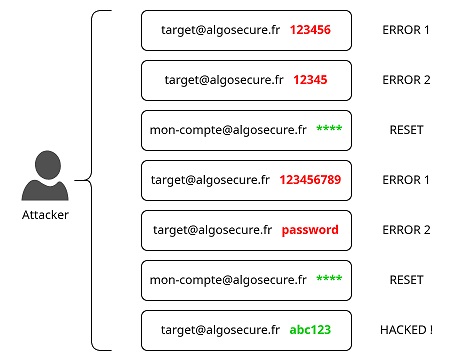
However, this technique requires a valid identifier on the target environment. It is particularly effective against misconfigured systems, where temporary account blocking or IP-based access bans are not uniformly applied, or are too lenient.
What to do then?
As we can see, solutions such as IP blocking, temporary account deactivation or multi-factor authentication (MFA) are not always sufficient: attackers can circumvent these measures using techniques such as botnets or social engineering. So it's important not to limit yourself to a single mechanism, but to reinforce security at all levels. By combining several defenses and thinking about possible means of circumvention. Combining several mechanisms considerably reduces the risk of a vulnerability being exploited.
À propos : Le blog d'AlgoSecure est un espace sur lequel notre équipe toute entière peut s'exprimer. Notre personnel marketing et commercial vous donne des informations sur la vie et l'évolution de notre société spécialisée en sécurité sur Lyon. Nos consultants techniques, entre deux tests d'intrusion ou analyses de risque, vous donnent leur avis ainsi que des détails techniques sur l'exploitation d'une faille de sécurité informatique. Ils vous expliqueront également comment sécuriser votre système d'informations ou vos usages informatiques particuliers, avec autant de méthodologie et de pédagogie que possible. Vous souhaitez retrouver sur ce blog des informations spécifiques sur certains sujets techniques ? N'hésitez pas à nous en faire part via notre formulaire de contact, nous lirons vos idées avec attention. Laissez-vous guider par nos rédacteurs : Alessio, Alexandre, Amine, Anas, Arnaud, Benjamin, Damien, Enzo, Eugénie, Fabien, Françoise, Gilles, Henri, Hicham, Jean-Charles, Jean-Philippe, Jonathan, Joël, Joëlie, Julien, Jéromine, Lucas, Ludovic, Lyse, Matt, Nancy, Natacha, Nicolas, Pierre, PierreG, Quentin, QuentinR, Sébastien, Tristan, Yann, Yannick, et bonne visite !